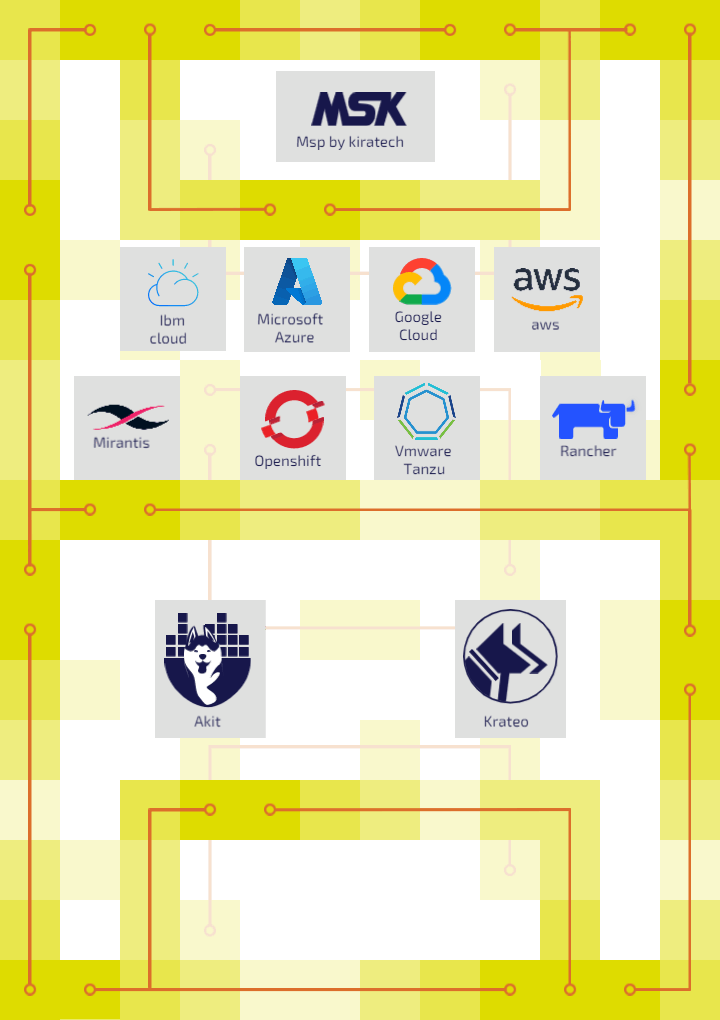
SOFTWARE SUPPLY CHAIN SECURED BY AKIT
CLOUD NATIVE CYBERSECURITY
The best IT security solutions from a Cloud Native perspective

ADVANTAGES
The advantages of AKIT
AKIT is the solution for security even for Enterprises, offering the following advantages:
- Reliability and security of Cloud and Open Source technologies for complete all-round security;
- Real-time monitoring for a rapid and proactive threat response by adopting and applying DevSecOps methodology;
- Shift-Left approach. (or Security-by-Design) with threats being detected and neutralised at their source.
CLOUD NATIVE SECURITY
In order to best implement the Cloud Native approach, it is crucial to adopt specific practices to support IT security. AKIT includes our Security services with a focus on:
- Cloud & Kubernetes Security. Secure your application infrastructure;
- Security Gate. Keep track of the actions taken along the software development path to sefeguard your security;
- DevSecOps. Identify and neutralise threats from the very beginning of the development process;
- VA|PT. Determine the weaknesses of your system and act promptly;
- IAM (Identity Access Management). Facilitate digital identity management and monitor access to and critical information within your organisation;
- Zero-Trust Security. Dynamic, identity-based security without a clear perimeter to migrate the risk of cyber-attacks in modern environments.
LEARN MORE ABOUT CYBERSECURITY
How Krateo PlatformOps integrates Backstage
Krateo PlatformOps, an open-source project developed by Kiratech's Cloud Native Dev Team, integrating Backstage, an open platform created by the...
(Lettura 4 minuti)
Useful DevOps Tools for a successful Reference Architecture
In the previous blog posts, we have deepened concepts like DevOps methodology, Cloud, Security and their connected tools and practices, by...
(Lettura 6 minuti)
ARGOMENTI:
DevOps
DevOps methodology in the Banking Industry
Today we live in a continuously technology, economic and politic evolving era, and the market players essentially need to adapt fast to this period...
(Lettura 4 minuti)
ARGOMENTI:
DevOps